🚨 200M+ Telegram User Records Allegedly Leaked — What This Means for Users
A post on a well-known data leak forum claims that more than 200 million Telegram user records have been exposed. The dataset allegedly includes usernames, phone numbers, and email addresses.
Telegram has publicly denied that private user data was compromised. However, cybersecurity researchers who reviewed a sample of the leaked data suggest the situation may be more complex.
What Was Reportedly Exposed?
According to researchers who analyzed a sample of the dataset shared by the attackers, the exposed information may include:
- Telegram usernames
- Full names
- Email addresses
- Phone numbers
- User IDs
The attackers claim the combined dataset contains over 200 million records, totaling approximately 44GB of uncompressed data.
At this time, it remains unclear whether this represents:
- A new Telegram data breach
- Previously scraped public data
- A compilation of older leaked databases
- Or a mixture of multiple sources
Duplicates may also exist in the dataset, which could reduce the actual number of unique affected users.
Telegram’s Response
Telegram stated that the leaked records appear to result from contact imports and contain only public user IDs and usernames.
According to the company, no private data was exposed, and users are not at risk.
However, researchers noted that email addresses and phone numbers are typically not publicly visible on Telegram unless users intentionally make them public. This raises questions about whether the dataset includes information from older breaches or external sources.
Why This Leak Matters
Even if part of the data was publicly accessible, data aggregation at scale significantly increases risk.
When attackers combine:
- Emails
- Phone numbers
- Usernames
They can launch:
- Mass phishing campaigns
- SMS phishing (smishing) attacks
- Social engineering operations
- Credential stuffing attempts
- Account takeover attacks
The larger the dataset, the easier it becomes to automate and scale these attacks globally.
The Bigger Cybersecurity Concern: Data Aggregation
Modern cyber threats often don’t rely on a single breach.
Instead, attackers collect and merge:
- Scraped public data
- Previously leaked databases
- Breach compilations
- Contact lists
Even if individual data points seem harmless, combined datasets become highly valuable for cybercriminals.
This case highlights how aggregation — not just breaches — represents a growing cybersecurity threat.
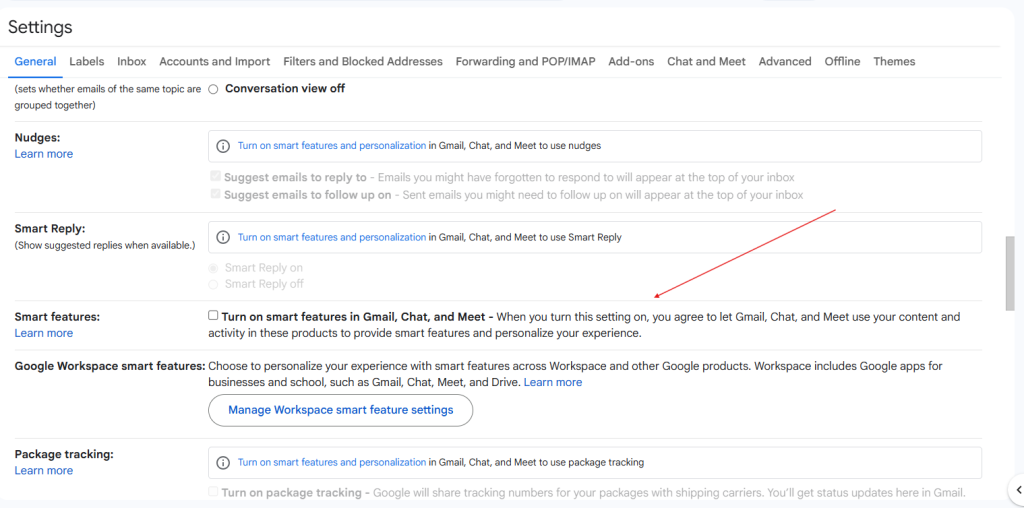
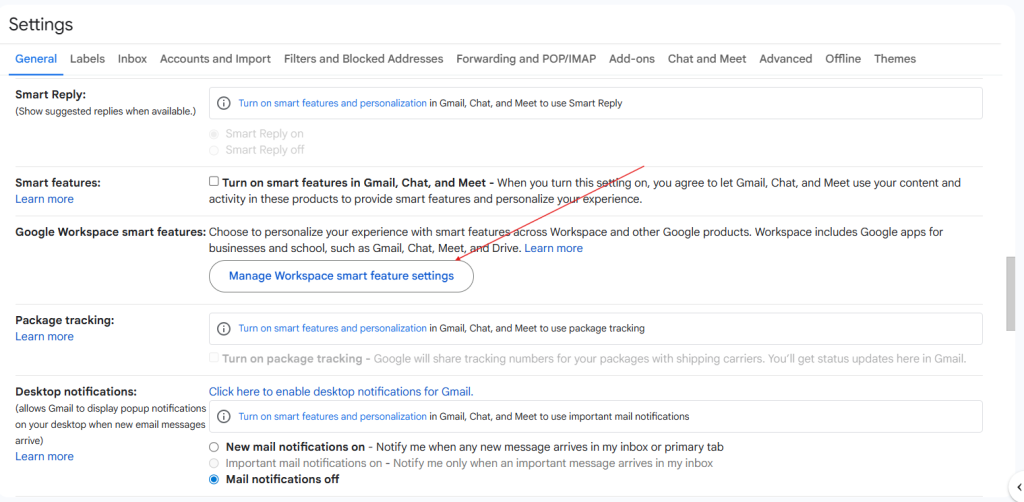
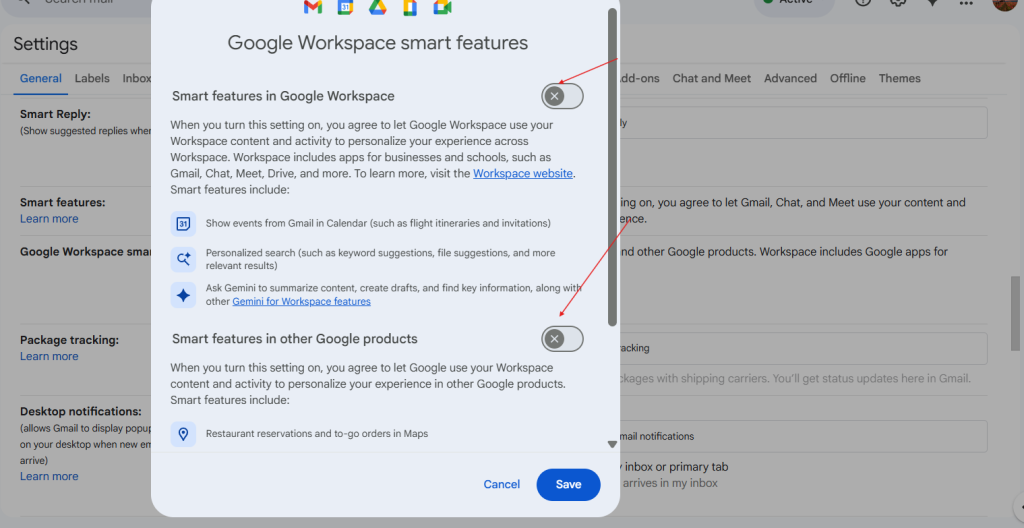
How Telegram Users Can Protect Themselves
If you use Telegram, consider taking these steps:
✅ Enable Two-Step Verification
✅ Hide your phone number in privacy settings
✅ Restrict who can find you by phone number
✅ Never share login verification codes
✅ Be cautious of suspicious links or messages
Users should remain alert for phishing attempts, especially following publicized leak announcements.
Final Thoughts
Whether this incident represents a new breach or a recycled dataset, the scale alone makes it concerning.
Messaging platforms remain high-value targets for threat actors. Proactive security habits are essential in today’s evolving threat landscape.
Staying informed and practicing strong digital hygiene can significantly reduce your risk.
Source: Reporting originally published by Cybernews (February 10, 2026). This article includes independent analysis and commentary.